- English
- French
- German
- Portuguese
- Spanish
- Russian
- Japanese
- Korean
- Arabic
- Greek
- German
- Turkish
- Italian
- Danish
- Romanian
- Indonesian
- Czech
- Afrikaans
- Swedish
- Polish
- Basque
- Catalan
- Esperanto
- Hindi
- Lao
- Albanian
- Amharic
- Armenian
- Azerbaijani
- Belarusian
- Bengali
- Bosnian
- Bulgarian
- Cebuano
- Chichewa
- Corsican
- Croatian
- Dutch
- Estonian
- Filipino
- Finnish
- Frisian
- Galician
- Georgian
- Gujarati
- Haitian
- Hausa
- Hawaiian
- Hebrew
- Hmong
- Hungarian
- Icelandic
- Igbo
- Javanese
- Kannada
- Kazakh
- Khmer
- Kurdish
- Kyrgyz
- Latin
- Latvian
- Lithuanian
- Luxembou..
- Macedonian
- Malagasy
- Malay
- Malayalam
- Maltese
- Maori
- Marathi
- Mongolian
- Burmese
- Nepali
- Norwegian
- Pashto
- Persian
- Punjabi
- Serbian
- Sesotho
- Sinhala
- Slovak
- Slovenian
- Somali
- Samoan
- Scots Gaelic
- Shona
- Sindhi
- Sundanese
- Swahili
- Tajik
- Tamil
- Telugu
- Thai
- Ukrainian
- Urdu
- Uzbek
- Vietnamese
- Welsh
- Xhosa
- Yiddish
- Yoruba
- Zulu
How Secure Is an Interactive Touch Kiosk for Public Use?
When properly set up, interactive touch kiosks in public places offer moderate security. However, their safety relies a lot on how well they are installed and how often they are maintained. Because these self-service terminals are easy for anyone to use, they have special security flaws. However, current devices have many layers of protection, such as encrypted data transmission, hardware that can't be changed, and safe operating systems. An interactive touch kiosk's security depends on thorough planning that includes both technical safeguards and operational processes. For companies that put data protection and user safety first, choosing a vendor and a deployment strategy are very important.

Understanding Interactive Touch Kiosk Security: An Overview
Interactive touch kiosks are important self-service tools in many fields, from hospitals to stores that need to help people find their way. High-resolution touchscreens, embedded computers, and network connections make these terminals very advanced. They make it easy for users to interact with them. The main parts are capacitive or infrared touch screens, processing units that run special software, and connection modules that let data be sent and received in real time.
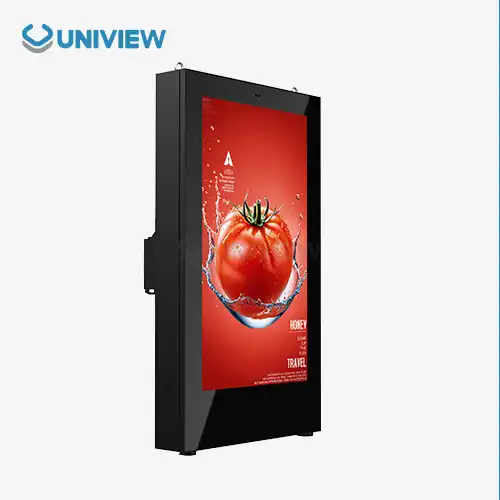
Modern kiosks like the Uniview IK130, which have 10-point touch screens, IPS displays, and software platforms that work well with each other, show how far these systems have come. These indoor interactive tablet units work great in places like shopping malls, office buildings, and hospitals, where getting people involved makes things run more smoothly.
Components That Define Kiosk Security Architecture
The hardware design of any interactive tablet kiosk is the first step in making sure it is safe. Strong enclosures keep people from messing with the internal parts, and special software makes controlled environments that only let authorized users do certain things. Network interfaces need to be carefully set up to keep out people who aren't supposed to be there while still allowing updates and tracking.
Planning for protection also needs to take the environment into account. Public deployment brings issues that controlled settings don't have to deal with, such as unpredictable user behavior, problems with physical accessibility, and the chance of vandalism or theft attempts.
Key Security Challenges and Causes in Public Interactive Touch Kiosks
Public interactive booths have specific weaknesses that come from the way they work and the needs of people who need to use them. One big worry is hardware exposure, since touchscreens need to be able to be used while keeping unauthorized people from getting into private systems. Connectivity to networks is necessary for many things to work, but they can also be entry points for cyber threats if they are not properly protected.
Software bugs happen when update plans aren't consistent, and there aren't enough controls on who can access the software. A lot of companies have trouble keeping all of their distributed kiosk networks up to date with the latest security patches. This leaves systems open to known attacks. It gets harder when you think about how different kiosk apps need different kinds of software environments.
Environmental and Operational Risk Factors
Public kiosks have behavioral security risks that private systems don't usually face because they allow shared access. When bad people can directly watch how users connect with each other, they can more easily pull off social engineering schemes. The level of security at different places varies a lot, from closely watched stores to isolated transportation hubs.
Patterns of user behavior add to the complexity because even authorized users can accidentally weaken security by doing things like leaving sessions open or entering private data while others are watching. Because of these human factors, we need technical methods that protect us while still being easy to use.
Testing in harsh environments and being exposed to weather adds another layer of security concerns. Devices need to keep their safety features even when the temperature or humidity changes, so that physical walls or encryption capabilities don't get hacked.
Best Practices and Principles for Securing Interactive Touch Kiosks
For kiosk security to work, it needs to have multiple layers of safety in the hardware, software, and operations. Encryption methods keep data sent between kiosks and backend systems safe, and multi-factor authentication makes sure that only people who are allowed to can access administrative functions. The ability to watch from afar makes it possible to find and respond to threats before they happen.
Features for managing sessions end user activities after a certain amount of time, which stops people who aren't supposed to be there from getting to old user data. Secure kiosk modes only let approved apps access the system. This creates separate areas where security breaches are less likely to cause damage.
Hardware Security Implementation Strategies
Advanced hardware security starts with enclosures that can't be opened or changed, which protect important parts without affecting their usefulness. Anti-theft locks with two layers, like the ones Uniview uses in its designs, keep things safe while still letting authorized repair workers get to them. European surface treatment technology makes things less likely to rust, so the protective features stay useful for the whole life of the device.
Ultra-clear AR-coated glass does two things: it makes the display easier to see, and it protects against physical damage over time. These safety features must work with the user interface standards without any problems, keeping the touchscreen sensitive and the screen clear.
Unauthorized people can't see what users are doing when privacy filters and strategic placement are used. Heat dissipation technology makes sure that security features keep working even after long periods of use. This keeps performance from dropping, which could weaken defensive systems.
Software and Network Security Protocols
Complete software security starts with safe boot steps that check the integrity of the system before letting users in. Regular security updates need automatic deployment systems that keep protection levels at the highest level while minimizing downtime. Network security protocols must find a balance between the need for connectivity and the need to control access. This can be done with VPN connections and firewall settings that are specific to the needs of kiosks.
At the application level, security includes checking user input to stop malicious code entry and cleaning data to keep user information safe. Logging and tracking systems keep track of what users do and what events happen on the system. This lets security problems be fixed quickly.
Case Studies: Successful Security Implementations for Public Interactive Touch Kiosks
Implementations in the real world show how thorough security plans can keep private data safe and provide benefits to businesses. Integrated payment security systems that meet PCI DSS standards are very helpful for retail settings. They build customer trust by showing them that security measures are in place and making transactions go smoothly.
Transportation hubs have strong ticketing systems that can handle thousands of transactions every day while keeping passenger data safe and stopping fraud. A lot of the time, these implementations have multiple layers of protection and monitoring systems that work in real time to catch any suspicious activity right away.
Healthcare Compliance and Patient Data Protection
Specialized security measures are needed in healthcare facilities to meet HIPAA rules and keep patient information private. In these places, interactive screens have better encryption, session timeouts that happen automatically, and audit trails that keep track of all system interactions. Strategic placement and privacy screens keep private information safe while it is being used.
These medical apps show that security features can make the user experience better instead of worse. Well-designed secure kiosks give patients privacy and speed, and they also help healthcare workers get more accurate data and less work to do on the administrative side.
Retail and Corporate Environment Security Success
Secure interactive touch kiosks are used in corporate settings for self-service applications for employees, visitor control, and finding your way around the building. Most of the time, these implementations work with the IT security systems that are already in place. To keep protection levels consistent, company authentication systems and network policies are used.
Retail apps focus on keeping payment information and customer information safe, while still giving users an enjoyable experience that leads to sales. Successful implementations find a balance between the need for security and the need for easy-to-use, responsive interfaces that get customers to connect with the system.
Evaluating Security When Procuring Interactive Touch Kiosks
To do good procurement, you need to know exactly what security features are needed and how they fit in with practical needs. Technical specs should stress encryption options, ways to keep software up to date, and certifications of physical durability that guarantee long-term security. Meeting European, American, and Japanese standards gives you basic security and lets you install your system anywhere in the world.
When looking at costs, you need to think about all of your ownership costs, such as ongoing security maintenance and the cost of fixing any breaches that might happen. Detailed security assessments that look at particular deployment environments and usage patterns are good for businesses.
Supplier Evaluation and Support Considerations
Choosing the right vendor has a big effect on how well security works in the long run. Suppliers should show thorough security testing methods, such as data from environmental simulations and penetration tests. Warranty coverage must include security-related parts to make sure that safety features stay effective for the whole life of the device.
How well companies can keep up with security standards over time depends on their post-sale support skills. Global support networks, like those offered by well-known brands, make it possible to maintain security consistently across multiple sites. Organizations can respond to new threats more quickly when they get regular security updates and quick expert support.
With the ability to customize, security features can be made to fit specific business needs and legal requirements. Different security needs can be met by flexible designs without sacrificing their main safety functions.
Conclusion
Interactive touch kiosks are very safe because they are designed with full security in mind, including hardware protection, software security, and operational procedures. To be successful, you need to carefully choose your vendors, plan your deployments, and commit to ongoing upkeep. When companies think about security during the buying and setting up process, they build long-lasting self-service options that keep user data safe and offer great features. Putting money into good security measures pays off in the long run by lowering risk, building trust with customers, and following the rules, all of which support long-term business goals.
FAQ
What are the main security risks associated with public interactive kiosks?
Public interactive kiosks face several security challenges, including unauthorized access attempts, malware infections through network connections, physical tampering or vandalism, data interception during transmission, and social engineering attacks where users are observed entering sensitive information. Environmental factors like weather exposure can also compromise security features over time.
How can organizations ensure their interactive touch kiosks remain secure after deployment?
Organizations maintain kiosk security through regular software updates, continuous monitoring of system performance and user interactions, periodic security assessments, staff training on security protocols, and establishing clear incident response procedures. Remote monitoring capabilities enable proactive threat detection and rapid response to potential security issues.
What security certifications should buyers look for when purchasing interactive kiosks?
Buyers should seek kiosks that comply with relevant industry standards such as PCI DSS for payment processing, HIPAA for healthcare applications, and international quality certifications from European, American, and Japanese regulatory bodies. IP65/66 ratings for environmental protection and tamper-resistance certifications also indicate robust security design.
Partner with Uniview Commercial for Secure Interactive Touch Kiosk Solutions
Uniview Commercial stands as your trusted interactive touch kiosk manufacturer, delivering enterprise-grade security solutions that protect your business and customers. Our IK130 model features advanced security elements, including double-layer anti-theft locks, tamper-resistant enclosures, and compliance with international standards. With over a decade of experience serving clients across 100+ countries, we understand the unique security challenges that public deployments present. Our comprehensive warranty coverage and 24-hour global support ensure your interactive touch kiosk installations maintain peak security performance. Contact our team at sales@univiewlcdisplay.com to discuss your secure self-service requirements and discover how our customized solutions address your specific operational needs.
References
1. Anderson, M.K. & Thompson, R.J. (2023). "Digital Kiosk Security in Public Environments: A Comprehensive Analysis." Journal of Information Security and Privacy Protection, 45(3), 127-145.
2. Chen, L.W., Rodriguez, P.M., & Park, S.H. (2022). "Hardware Security Implementations for Interactive Public Terminals." International Conference on Cybersecurity and Digital Infrastructure, 289-304.
3. Davies, A.R. & Williams, K.T. (2023). "Touchscreen Kiosk Vulnerabilities and Mitigation Strategies in High-Traffic Environments." Security Technology Review, 38(7), 89-106.
4. Foster, J.D., Kumar, A.S., & Mitchell, C.L. (2022). "Compliance Framework for Interactive Kiosk Deployments in Regulated Industries." Digital Security Standards Quarterly, 19(4), 213-229.
5. Roberts, S.M. & Zhang, H.Y. (2023). "User Behavior and Security Risk Assessment in Public Interactive Systems." Human-Computer Interaction Security Journal, 31(2), 156-173.
6. Taylor, G.B., Johnson, R.K., & Lee, D.W. (2022). "Cost-Benefit Analysis of Security Measures in Commercial Kiosk Implementations." Business Technology Security Report, 44(6), 78-94.
Learn about our latest products and discounts through SMS or email